
Wireshark Crack + License Key Free Download
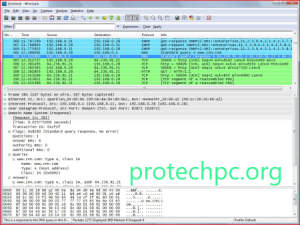
Wireshark Crack is the most important and widely used network protocol analyzer in the world. It allows you to see what’s happening on your network at a microscopic level and is the de facto (and often de jure) standard in many commercial and non-profit companies, government agencies, and educational institutions. Few tools are as useful to the IT professional as Wireshark, the network packet capture tool. Wireshark will help you capture network packets and display them at a granular level. Once these packets are broken down, you can use them for real-time or offline analysis. This tool allows you to put your network traffic under a microscope and then filter and dig deeper, getting closer to the root cause of problems, helping with network analysis and ultimately network security. This free Wireshark tutorial will teach you how to capture, interpret, filter, and inspect data packets for effective troubleshooting.
Wireshark is a network protocol analyzer or an application that captures packets from a network connection, such as from your computer to your home office or the Internet. The packet is the name given to a discrete unit of data on a typical Ethernet network. Wireshark is the most widely used packet sniffer in the world. Like any other packet sniffer, Wireshark does three things:
Packet Capture: Wireshark listens to a network connection in real time and then captures entire streams of traffic, possibly tens of thousands of packets at a time.
Filtering: Wireshark is able to slice and dice all this random data live using filters. By applying a filter, you can get only the information you need to see.
Visualization: Wireshark, like any good packet sniffer, allows you to dive right into the heart of a network packet. It also allows you to view entire conversations and network flows.
Wireshark is a Tool to Understand Network Traffic Analysis and Packet Detection
Packet sniffing can compare to caving: going into a cave and hiking. People who use Wireshark on a network are like those who use flashlights to see what interesting things they can find. After all, when you use Wireshark on a network connection (or a flashlight in a cave), you’re effectively using a tool to search for tunnels and tubes to see what you can see. Wireshark’s development thrives on voluntary contributions from networking experts around the world and is the continuation of a project started by Gerald Combs in 1998.
Wireshark has many uses, including troubleshooting networks that have performance issues. Cybersecurity professionals often use Wireshark to trace connections, view the content of suspicious network transactions, and identify bursts of network traffic. It’s an important part of any IT professional’s toolkit, and hopefully, the IT professional has the knowledge to use it. Wireshark is a security tool used by government agencies, educational institutions, corporations, small businesses, and non-profit organizations to troubleshoot network issues. Additionally, Wireshark can be used as a learning tool.
Those who are new to information security can use Wireshark as a tool to understand network traffic analysis, how communication takes place when particular protocols are involved, and where it fails when certain problems occur. Regardless of the packages monitored, you can export the results in XML, CSV, TXT, or PostScript and use other third-party tools to analyze them. For your convenience, the tool also supports decryption, reading, and writing in multiple formats, as well as a powerful macro system.

Features:
- Deep inspection of hundreds of protocols, with more being added all the time
- Live capture and offline analysis
- Standard three-pane package browser
- Cross-platform – runs on Windows, Linux, macOS, Solaris, FreeBSD, NetBSD, and many others
- Captured network data can be explored through a GUI or through the TShark utility in TTY mode
- The most powerful display filters in the industry
- Full VoIP Analysis
- Read/write many different capture file formats: tcpdump (libpcap), Pcap NG, Catapult DCT2000, Cisco Secure IDS iplog, Microsoft Network Monitor, Network General Sniffer® (compressed and uncompressed), Sniffer® Pro and NetXray®, Network Instruments Observer, NetScreen snoop, Novell LANalyzer, RADCOM WAN/LAN Analyzer, Shomiti/Finisar Surveyor, Tektronix K12xx, Visual Networks Visual UpTime, WildPackets EtherPeek/TokenPeek/AiroPeek, and many others
- Live data can be read from Ethernet, IEEE 802.11, PPP/HDLC, ATM, Bluetooth, USB, Token Ring, Frame Relay, FDDI, and others (depending on your platform)
- Decryption support for many protocols including IPsec, ISAKMP, Kerberos, SNMPv3, SSL/TLS, WEP, and WPA/WPA2
- Color rules can apply to the list of packages for quick and intuitive analysis
Additional Wireshark Features:
Beyond capturing and filtering, there are other features in Wireshark that can make your life better.
Wireshark Coloring Options
You can configure Wireshark to color your packets in the Packet List according to the display filter, allowing you to emphasize the packets that you want to highlight. See some examples here.
Wireshark Promiscuous Mode
By default, Wireshark only captures packets going to and from the computer, it is running on. By checking the box to run Wireshark in promiscuous mode in the capture settings, you can capture most of the traffic on the LAN.
Wireshark Command Line
Wireshark provides a command-line interface (CLI) if you are operating a system without a GUI. The best practice would be to use the CLI to capture and save a log so that you can review the log with the GUI.
Metrics and Statistics
Under the Statistics menu item, you will find a host of options to display details about your catch.
What’s New?
Bug Fixes
The following vulnerabilities were fixed:
- WNBA-sec-2022-01 RTMPT dissector infinite loop. Edition 17813.
- WNBA-sec-2022-02 Large loops on various dissectors. Number 17829, Number 17842, Number 17847, Number 17855, Number 17891, Number 17925, Number 17926, Number 17931, Number 17932, Number 17933.
- WNBA-sec-2022-03 PVFS dissector crash. Edition 17840.
- WNBA-sec-2022-04 CSN.1 dissector accident. Edition 17882.
- WNBA-sec-2022-05 CMS dissector crash. Edition 17935.
The following bugs were fixed:
- Support for GSM SMS TPDU in HTTP2 body Issue 17784.
- Wireshark broke the ABI by removing ws_log_default_writer from libwsutil Issue 17822.
- Fedora RPM package build fails with RPATH of /usr/local/lib64 Issue 17830.
- macOS-setup.sh: ftp.pcre.org no longer exists Issue 17834.
- org/no cap → npcap.com: domain/URL change issue 17838.
- MPLS ECHO FEC stack change TLV not parsed correctly Issue 17868.
- Attempting to open a system journal export file with segment errors Issue 17875.
- Dissector error in 802.11ac packets Issue 17878.
- The information column shows only one NGAP/S1AP packet out of multiple packets within one SCTP packet Issue 17886.
- Uninstalling Wireshark 3.6.2 on Windows 10 does not remove the installation directory because it does not remove the User Guide subdirectory and all of its contents. Edition 17898.
- 6 does not compile without Zlib Issue 17899.
- SIP statistics no longer correctly report method-type accounting issue 17904.
- Fuzz job failure output: fuzz-2022-01-26-6940.pcap Issue 17909.
- Broken SCTP relay detection for the first data chunk of each association with relative TSN problem 17917.
- “Show in folder” does not work correctly for filenames with spaces Issue 17927.
Updated capture file support: BLF and libcap
System Requirements:
Microsoft Windows
- Windows 10, 8.1, Server 2019, Server 2016, Server 2012 R2, and Server 2012.
- The Universal C Runtime. This included Windows 10 and Windows Server 2019 and on earlier versions of Microsoft Windows Update enabled. Otherwise, you must install KB2999226 or KB3118401.
- Any modern AMD64/x86-64 64-bit or x86 32-bit processor.
- 500 MB of RAM available. Larger capture files require more RAM.
- 500 MB of available disk space. Capture files require additional disk space.
- Any modern screen. A resolution of 1280 × 1024 or higher. Wireshark will use HiDPI or Retina resolutions if available. Advanced users will find multiple monitors useful.
- A compatible network card to capture
- or Ethernet. Any Windows-compatible card should work. See the wiki pages on Ethernet capture and offload for issues that may affect your environment.
- See the Wireshark wiki page. Capturing raw 802.11 information can be difficult without special equipment.
Mac OS
- Wireshark is compatible with macOS 10.13 and later.
- 3.4 was the last branch release to support macOS 10.12.
- Wireshark 2.6 was the last branch release to support Mac OS X 10.6 and 10.7 and OS X 10.8 to 10.11.
- 2.0 was the last branch release to support OS X on Intel 32-bit.
- Wireshark 1.8 was the last branch release to support Mac OS X on PowerPC
How to install it?
- Open a web browser.
- Select Download Wireshark.
- Select the Wireshark Windows installer that matches your system type, either 32-bit or 64-bit, as determined in the Activity
- Save the program to the Downloads folder.
- Close the web browser.
- Click on Install.
- Follow The Instructions.
- Must visit this site for All Software cracks
Activation Keys
DVEFHS-RUFYGB-RFGCVR-RUYGUW WIUWR-FBVRVR-RUVBNC-EUHFRBR ESFGCV-EADGSXC-SFHC-ASFHXB SFHX-WRYSFG-WRYFGVB-RETDHG
Wireshark Crack + License Key Free Download From The Link Given Below